iGPT vs Threat Watch
Side-by-side comparison to help you choose the right AI tool.
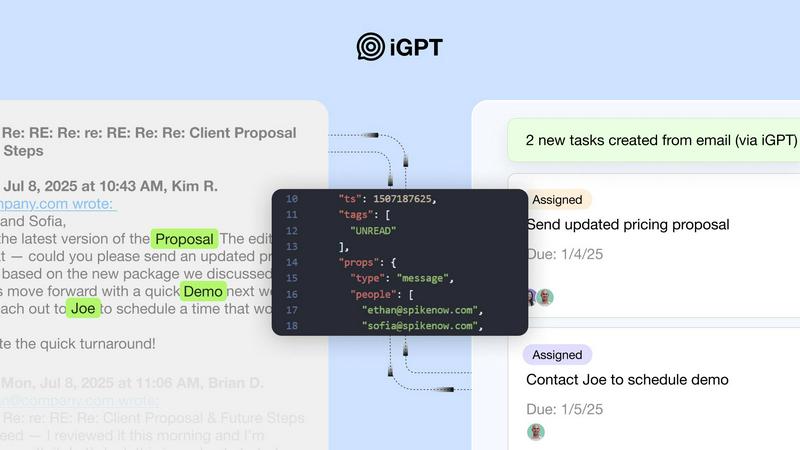
iGPT turns email chaos into smart answers, empowering agents with seamless, context-aware insights in real-time.
Last updated: February 26, 2026
Threat Watch
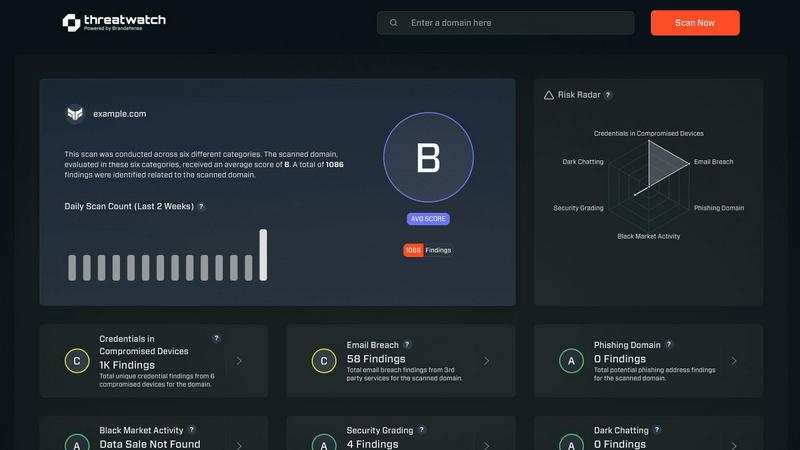
Reclaim your cyber safety with Threat Watch, the fast way to spot risks and secure your digital domain.
Last updated: February 26, 2026
Visual Comparison
iGPT
Threat Watch
Feature Comparison
iGPT
Immediate Integration
Get up and running in no time with iGPT's SDK and live playground, allowing you to test requests and responses quickly. Immediate integration means you can dive right into the action without unnecessary delays.
Unified Endpoint
Simplify your workflow with a single API call that handles retrieval, context shaping, and reasoning all in one seamless pipeline. This unified approach eliminates the chaos of juggling multiple endpoints, making your life a lot easier.
Real-time Ingestion
iGPT indexes new messages and attachments instantly, ensuring you always have access to the most current data. This real-time processing keeps your information fresh and relevant, so you never miss a beat.
Cited Answers
Every response from iGPT links back to the original messages and attachments, giving you the source context you need for thorough understanding and transparency. This feature is crucial for accountability and traceability in enterprise communications.
Threat Watch
Real-Time Threat Intelligence
Stay ahead of the curve with real-time threat intelligence that alerts you to vulnerabilities as they emerge. No more waiting for the storm to hit; you’ll know exactly what’s coming and how to dodge it.
Comprehensive Asset Evaluation
Threat Watch evaluates your critical security categories, giving you a full-spectrum view of your assets. Identify potential weak points and bolster your defenses, ensuring that no stone is left unturned in your security strategy.
Dark Web Monitoring
Don’t let your sensitive data be the next hot commodity on the dark web. Our monitoring feature scans the underbelly of the internet for compromised information, alerting you before it can be exploited.
Phishing Protection
Catch those sneaky phishing attempts before they snag your users. With advanced algorithms that detect suspicious addresses, Threat Watch ensures your team remains safe from deceptive traps that can lead to data breaches.
Use Cases
iGPT
Email Assistants
Harness the power of iGPT to create intelligent email assistants that can draft responses, prioritize tasks, and act on communications with full contextual awareness. This boosts productivity and ensures nothing falls through the cracks.
Workflow Automation
Transform lengthy email threads into actionable tasks, deadlines, and approvals effortlessly. iGPT helps you flag what's stuck in the process, streamlining your operations and enhancing team collaboration.
Support Copilots
Reconstruct the complete customer narrative across long email chains, diverse attachments, and shifts in tone. With iGPT, support agents can provide tailored, context-aware responses that resonate with customers.
Compliance and Audit Trail
Maintain a robust audit trail of feedback, approvals, and rationales rooted in original conversations. iGPT empowers organizations to trace decisions back to their source, ensuring compliance and transparency in every interaction.
Threat Watch
Small Business Security
Small businesses often lack the resources for extensive cybersecurity measures. Threat Watch provides these companies with the tools they need to identify vulnerabilities and secure their digital assets without breaking the bank.
Enterprise Risk Management
For large organizations, managing risk is paramount. Threat Watch delivers comprehensive insights into potential threats across vast networks, enabling risk managers to prioritize and tackle vulnerabilities efficiently.
Incident Response Preparation
When a cyber incident occurs, time is of the essence. Threat Watch equips security teams with the intelligence needed to respond quickly and effectively, minimizing damage and recovery time.
Compliance Assurance
Navigating the maze of compliance regulations can be daunting. Threat Watch helps organizations maintain compliance with industry standards by continuously monitoring for potential risks and breaches, ensuring you stay on the right side of the law.
Overview
About iGPT
Welcome to the cutting-edge world of email intelligence with iGPT, the API that redefines how enterprises interact with their email data. Say goodbye to the chaos of unstructured information and hello to a realm where every email and attachment transforms into actionable insights. Designed for organizations that thrive on data, iGPT provides a robust, secure, and auditable gateway for AI-powered systems to delve deep into email conversations. With iGPT, you can effortlessly extract context-aware answers, enhancing workflows and decision-making across various sectors like sales, HR, and compliance. No more tedious parsing or messy data—iGPT captures, indexes, and makes every interaction accessible in real-time. Elevate your operations with clarity, compliance, and a newfound confidence in navigating the complexities of communication data.
About Threat Watch
Welcome to the cutting edge of cybersecurity with Threat Watch! This all-in-one intelligence powerhouse is designed to keep your digital domain locked down tighter than Fort Knox. Picture this: a tool that doesn’t just scratch the surface but dives deep into the nitty-gritty of your organization’s assets, vulnerabilities, and exposures. Threat Watch offers a crystal-clear picture of your cyber health, illuminating the dark corners where threats might lurk. It’s not just about keeping you safe; it’s about handing you the reins to your cybersecurity. With real-time insights, you can snag critical intel on compromised devices, breached accounts, phishing addresses, and even murky dark web contents. Whether you're a business owner, an IT whiz, or a security team member, this tool is your go-to for serious defense against cyber threats. Uncover your cybersecurity health faster than ever and stay steps ahead of the game by identifying, prioritizing, and zapping risks with unmatched speed and precision. Get ready to take control of your cyber destiny.
Frequently Asked Questions
iGPT FAQ
How does iGPT ensure data security?
iGPT prioritizes enterprise-grade protection by employing zero data training, role-based access control, and zero data retention. This means your data is never used for model training, securely handled, and processed in memory without storage.
Can iGPT handle attachments?
Absolutely! iGPT excels at extracting text, data, and structure from various document types, including PDFs and spreadsheets. This capability ensures that you can gather insights from all relevant files linked to your email conversations.
Is there a limit to the number of emails iGPT can process?
iGPT is designed to handle large volumes of email data efficiently. With real-time indexing and hybrid retrieval methods, it can process extensive email threads and attachments without compromising performance.
How quickly can I expect responses from iGPT?
iGPT is optimized for speed, delivering responses with an average retrieval time of around 200ms and reaching the first token in approximately 3 seconds, even across large, messy datasets. This ensures you get the information you need without unnecessary delays.
Threat Watch FAQ
What types of threats can Threat Watch identify?
Threat Watch can identify a variety of threats, including compromised devices, breached accounts, phishing attempts, and dark web exposures, providing you with a comprehensive view of your cybersecurity landscape.
How does Threat Watch monitor the dark web?
Our dark web monitoring feature scans numerous underground sources to identify if any of your sensitive information has been leaked or sold. You'll receive alerts if anything concerning is discovered.
Is Threat Watch suitable for small businesses?
Absolutely! Threat Watch is designed to be scalable, making it perfect for small businesses that need robust cybersecurity without the hefty price tag.
How often does Threat Watch update its threat intelligence?
Threat Watch provides real-time updates, ensuring that you are always aware of the latest threats and vulnerabilities affecting your organization, allowing you to take immediate action when necessary.
Alternatives
iGPT Alternatives
iGPT is the revolutionary API that takes the hassle out of email communication, turning chaos into clarity. As a leader in the Business Intelligence category, it empowers enterprises to extract smart, contextual answers from their email conversations, ensuring that every interaction is captured and indexed. It’s a game-changer for teams that demand data-driven insights and streamlined operations. Users often seek alternatives to iGPT for various reasons, including pricing structures, feature sets, and compatibility with existing platforms. When exploring options, it's essential to consider factors like usability, security, and the ability to integrate seamlessly with your current systems. The right choice will not only meet your operational needs but also enhance your overall productivity and decision-making capabilities.
Threat Watch Alternatives
Threat Watch is your go-to powerhouse for cybersecurity intelligence, designed to instantly assess your organization’s cyber health while keeping threats at bay. It belongs to the Business Intelligence category, offering users real-time insights into vulnerabilities, exposures, and compromised assets. However, as with any product, users often seek alternatives due to factors like pricing, specific features, or compatibility with their existing platforms and workflows. When on the hunt for an alternative, prioritize solutions that align with your unique security needs, budget constraints, and the ability to integrate seamlessly into your tech stack without missing a beat. --- [{"question": "What is Threat Watch?", "answer": "Threat Watch is an advanced cybersecurity tool that assesses your organization's cyber health by providing insights into vulnerabilities, compromised devices, and more."}, {"question": "Who is Threat Watch for?", "answer": "Threat Watch is designed for businesses, IT professionals, and security teams who are serious about defending against cyber threats."}, {"question": "Is Threat Watch free?", "answer": "Threat Watch is a premium service that offers powerful cybersecurity insights, typically requiring a subscription for full access."}]