Pro Cursor Rules vs RedVeil
Side-by-side comparison to help you choose the right AI tool.
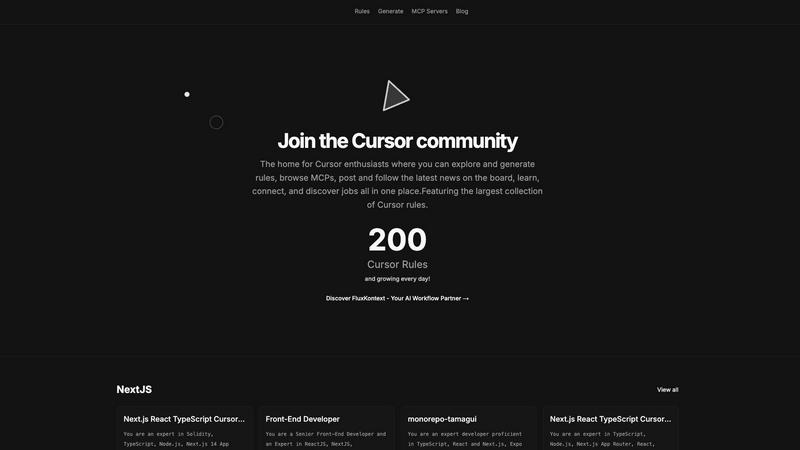
Pro Cursor Rules
Unleash your creativity in the ultimate Cursor hub to explore, generate rules, and connect with a thriving community.
Last updated: February 26, 2026
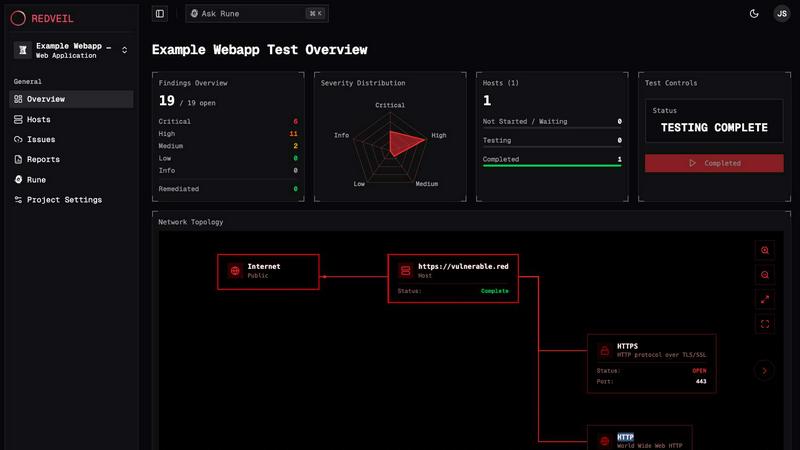
RedVeil
RedVeil delivers lightning-fast AI-powered penetration testing to expose vulnerabilities and streamline your security.
Last updated: February 28, 2026
Visual Comparison
Pro Cursor Rules
RedVeil
Feature Comparison
Pro Cursor Rules
Extensive Library of Cursor Rules
Explore an impressive collection of 151 cursor rules designed to cater to every style and preference. Whether you want something sleek and modern or quirky and fun, our library has got you covered. This feature allows you to experiment and find the perfect cursor that reflects your personality and enhances your digital experience.
Community Interaction
Engage with an inclusive community of cursor enthusiasts who share your passion. Participate in discussions, share your creations, and get feedback from like-minded individuals. The community interaction feature allows you to connect, collaborate, and learn from others, making your cursor customization journey even more enriching.
Job Opportunities Board
Looking to turn your cursor creativity into a career? Our platform features a job opportunities board where you can discover exciting job openings in the world of digital design and development. This unique feature not only connects you with potential employers but also helps you network within the industry, opening doors to new possibilities.
Latest News and Updates
Stay in the loop with the latest trends, updates, and innovations in cursor customization. Our news board keeps you informed about new releases, community highlights, and industry insights. This feature ensures you’re always at the forefront of cursor design, empowering you to continually evolve your style.
RedVeil
AI-Driven Penetration Testing
RedVeil harnesses the power of artificial intelligence to conduct penetration tests that mimic real-world attacks. In minutes, you can initiate a test that identifies exploitable vulnerabilities with precision and clarity, giving your team the insights needed to bolster security.
One-Click Retesting
Once vulnerabilities are remediated, the last thing you want is to wait ages to see if your fixes worked. With RedVeil's One-Click Retesting feature, you can rapidly verify changes without delays. It's all about keeping your security posture agile and responsive.
Audit-Ready Reports
Navigating compliance requirements is a breeze with RedVeil. Generate professional, audit-ready reports at the click of a button, tailored for various standards like SOC 2, ISO 27001, and PCI-DSS. These reports are designed for executives, engineers, and security teams alike.
Guided Remediation
RedVeil doesn’t just highlight issues; it provides context, reproduction steps, and tailored remediation guidance. This means your team can understand the vulnerabilities, why they matter, and how to fix them effectively, making security a collaborative effort.
Use Cases
Pro Cursor Rules
Personalizing Your Workspace
Transform your mundane digital workspace into a visually stunning environment. With Pro Cursor Rules, you can create a cursor that resonates with your personal style, making your daily tasks more enjoyable and inspiring. Personalization is key to productivity, and a unique cursor can be your secret weapon.
Enhancing User Experience
Web developers and designers can leverage Pro Cursor Rules to enhance user experience on their websites. By incorporating custom cursors that align with the site’s theme, you can create a more immersive and engaging experience for users. This attention to detail can significantly improve site interaction and retention.
Showcasing Creativity in Projects
Whether you're a student working on a project or a professional looking to impress clients, Pro Cursor Rules allows you to showcase your creativity. Custom cursors can add a unique flair to any presentation or design project, setting you apart from the competition and making a lasting impression.
Joining Collaborative Projects
Engage in collaborative design projects with other community members. Pro Cursor Rules provides a platform where you can team up with others to create innovative cursor designs. This collaborative aspect not only boosts creativity but also fosters relationships that can lead to future opportunities in the digital design space.
RedVeil
Agile Development Teams
For software development teams that deploy updates frequently, RedVeil allows them to conduct penetration tests on-demand, ensuring that each release is secure without disrupting their workflow.
Compliance and Auditing
Organizations aiming for compliance can leverage RedVeil's audit-ready reports to meet regulatory requirements efficiently. The fast turnaround allows them to stay ahead in their compliance journey.
Security Awareness Training
Use RedVeil to simulate real-world attacks and educate your team on vulnerabilities. This hands-on approach helps foster a culture of security awareness within your organization.
Continuous Security Posture Management
With RedVeil, security is not a once-a-year checklist item. Organizations can regularly test their environments as changes occur, ensuring that security is maintained without the hassle of scheduling.
Overview
About Pro Cursor Rules
Welcome to the future of cursor customization with Pro Cursor Rules! This dynamic platform is your ultimate playground, whether you're just starting your journey or you're a cursor customization veteran. Dive into our extensive library of 151 unique cursor rules that empower you to create a digital experience that’s as unique as you are. With Pro Cursor Rules, you're not just modifying cursors; you're expressing your individuality in vibrant, creative ways. Our platform fosters a thriving community where you can connect with fellow cursor enthusiasts, share ideas, and stay updated on the latest trends. Plus, explore job opportunities in the burgeoning field of digital design. Join us in this cursor revolution and transform the way you interact with your screens. The possibilities are endless, and the only limit is your imagination!
About RedVeil
RedVeil is the revolutionary AI-powered penetration testing tool that’s ditching the old-school, tedious methods of security assessments. With the software's lightning speed and human-like reasoning, it empowers modern engineering teams to secure their applications in real-time. Gone are the days of waiting weeks for a consultant and shelling out tens of thousands for a single "point-in-time" test that quickly becomes obsolete. RedVeil offers an agile solution that spins up full, autonomous penetration tests in mere minutes, delivering actionable, audit-ready reports by the afternoon. Designed for software teams who deploy code daily, RedVeil ensures security is integrated into your workflow, allowing you to focus on building great products without the fear of vulnerabilities lurking in the shadows.
Frequently Asked Questions
Pro Cursor Rules FAQ
What is Pro Cursor Rules?
Pro Cursor Rules is a platform dedicated to cursor customization, offering a wide range of cursor rules and a vibrant community for enthusiasts to connect, share, and learn.
How do I create a custom cursor?
Creating a custom cursor is easy! Simply explore our library of rules, select the ones you like, and follow the prompts to personalize each cursor to suit your unique style.
Can I join the community without signing up?
While you can browse some content, signing up is necessary to fully engage with the community, post updates, and access all features, including job listings and custom rule generation.
Are there any costs associated with using Pro Cursor Rules?
Pro Cursor Rules is primarily free to use, with access to a plethora of cursor rules and community features. However, some advanced features may require a subscription, which will be clearly outlined on the platform.
RedVeil FAQ
Does RedVeil perform a real penetration test?
Absolutely! RedVeil conducts comprehensive penetration tests using advanced AI algorithms that simulate real attacker behavior, ensuring that you receive authentic vulnerabilities and actionable insights.
How many penetration tests can I do with my annual subscription?
Your subscription allows for unlimited penetration tests, so you can test as often as you need without worrying about additional costs. This flexibility is crucial for maintaining a strong security posture.
Is there a chance that my web application or network could go down during the test?
RedVeil is designed to minimize risks while testing, focusing on real exploitable risks without compromising the availability of your services. We prioritize safety during all assessments.
Can I use RedVeil's penetration test reports to meet the requirements of my compliance?
Yes! RedVeil's reports are specifically tailored to meet the requirements of various compliance standards, making them perfect for auditors and compliance teams alike.
Alternatives
Pro Cursor Rules Alternatives
Pro Cursor Rules is the ultimate hub for cursor customization enthusiasts, allowing users to explore and generate unique cursor rules that add a personal touch to their digital experience. This platform is all about creativity and connection, serving as a vibrant community for newbies and pros alike. As users dive into the world of cursor customization, they often find themselves seeking alternatives due to various reasons like pricing, feature sets, or compatibility with different platforms. When choosing an alternative, it's essential to consider factors such as user experience, community engagement, and the variety of customization options available to ensure a fulfilling experience.
RedVeil Alternatives
RedVeil is an innovative AI-powered penetration testing tool designed to revolutionize how security assessments are conducted. By leveraging cutting-edge artificial intelligence, it empowers teams to expose vulnerabilities in real-time, ensuring that security is woven into the fabric of the development process. Users often seek alternatives to RedVeil due to various reasons such as pricing structures, specific feature sets, or compatibility with their existing platforms. When searching for an alternative, it's crucial to consider factors like the speed of testing, the comprehensiveness of reports, the ease of use, and how well it integrates with your current workflows. Look for solutions that offer actionable insights and cater to your unique security needs, ensuring that you're not just getting a tool, but a partner in your security journey.
